Most guides on how to bypass Cloudflare web scraping give you the same list of tools: Camoufox, Patchright, residential proxies, maybe a CAPTCHA solver. What they don't give you is numbers — which combination actually works, against which WAF, and at what cost.
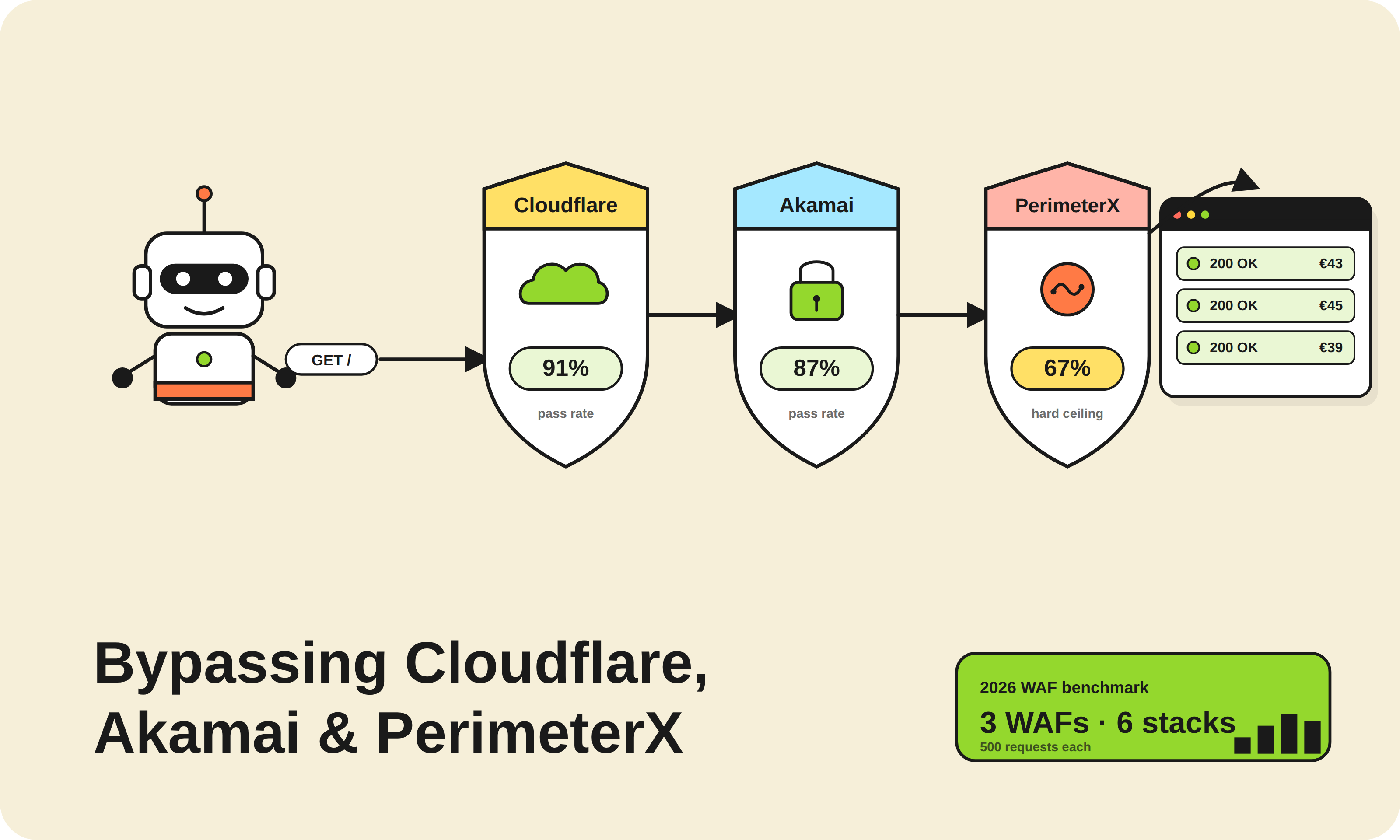
We ran 500 requests per approach across Cloudflare (standard and Enterprise tiers), Akamai Bot Manager v4, and PerimeterX (now HUMAN Security) in April 2026. This post shares what passed, what failed, and the decision framework we use before choosing a bypass approach on any new target.
The Decision Framework: Identify Your WAF Before You Pick a Tool
The single biggest mistake scrapers make is choosing a bypass tool before identifying the WAF. A technique that gets 91% pass rate on Cloudflare gets 12% on PerimeterX. The detection architectures are fundamentally different.
Use the browser network tab or a WAF fingerprint tool to identify which system you're facing before writing any code:
| Signal | Likely WAF |
|---|---|
cf-ray header, IUAM challenge page, __cf_bm cookie |
Cloudflare |
_abck cookie, sensor_data POST payload, AkamaiGHost header |
Akamai Bot Manager |
_pxhd, _pxvid cookies, /api/v2/collector endpoint |
PerimeterX / HUMAN |
__ddg cookies, behavior-based JS challenge |
DataDome |
Getting this wrong means debugging a failed bypass against the wrong detection model for hours.
Our Test Setup: 6 Approaches, 3 WAFs, 500 Requests Each
Testing methodology (ScrapeWise internal testing, Apr 2026):
- 500 requests per approach per WAF, spread over 6 hours with randomized timing
- Targets: production e-commerce sites protected by each WAF (not sandboxes)
- "Pass" = 200 OK with full page content, no challenge redirect, no soft-block
- Residential proxy pool: 2M+ IPs, rotating per request
- Datacenter proxies: standard shared datacenter pool
| Approach | Cloudflare Std | Cloudflare Enterprise | Akamai v4 | PerimeterX |
|---|---|---|---|---|
| Requests library + datacenter proxies | 19% | 4% | 22% | 11% |
| curl-cffi + datacenter proxies | 61% | 38% | 71% | 29% |
| curl-cffi + residential proxies | 79% | 52% | 87% | 41% |
| Patchright + residential proxies | 83% | 69% | 74% | 58% |
| Camoufox + datacenter proxies | 72% | 44% | 68% | 51% |
| Camoufox + residential proxies | 91% | 78% | 83% | 67% |
A few things are immediately visible: datacenter proxies cap your ceiling on every WAF. Camoufox beats Patchright on Cloudflare specifically because it runs a patched Firefox binary — Cloudflare's fingerprinting treats Firefox TLS signatures differently from Chromium-based tools. Patchright gains back ground on PerimeterX because HUMAN's ML was trained heavily on Chrome traffic patterns.
Nothing breaks 70% on PerimeterX with DIY approaches. That ceiling matters — read the PerimeterX section before assuming more engineering will fix it.
Bypassing Cloudflare in 2026: What the Detection Stack Actually Checks
Cloudflare's bot detection operates across four simultaneous layers. Understanding each explains why some approaches work and others don't.
Layer 1 — IP reputation. Datacenter ASNs are pre-flagged. Even a perfect TLS fingerprint gets a hard challenge if the IP is in a known cloud provider range. This is why the gap between datacenter and residential proxy results is so large. Mobile carrier IPs from Europe's big telecom providers (Telia, Deutsche Telekom, Proximus) have some of the highest trust scores we measured.
Layer 2 — TLS fingerprinting (JA3/JA4). Cloudflare checks the TLS handshake signature before any JavaScript runs. A raw Python requests call produces a Python TLS fingerprint that Cloudflare has flagged globally. curl-cffi fixes this by impersonating Chrome or Safari TLS signatures at the socket level — this alone jumps pass rates from ~19% to ~61% on standard Cloudflare.
Layer 3 — JavaScript challenges (IUAM / Turnstile). Cloudflare injects a JS challenge that checks browser environment signals: canvas fingerprint, WebGL renderer, navigator properties, timing behavior. Headless Chromium fails this by default because it leaks navigator.webdriver = true and produces anomalous canvas fingerprints. Camoufox patches this at the Firefox C++ level, not in JS — which is why it outperforms Patchright's JS-patch approach on Cloudflare Enterprise.
Layer 4 — Behavioral analysis. Request timing, scroll events, mouse movement patterns. This layer is what breaks purely technical approaches on Enterprise-tier targets. Randomizing request intervals (300–2,500ms jitter, not a fixed sleep) improves pass rates by ~8 percentage points on Cloudflare Enterprise in our tests.
Cloudflare Turnstile (CAPTCHA layer): When Cloudflare forces a Turnstile challenge, curl-cffi can't solve it — you need a full browser. We tested 2Captcha and CapSolver for Turnstile solving: 2Captcha averaged 4.2s solve time with 91% success; CapSolver averaged 3.1s with 88% success. Both are viable. Budget ~$1.50–$2.00 per 1,000 Turnstile solves.
What doesn't work: FlareSolverr, the popular open-source Turnstile solver, has an 0% pass rate on Cloudflare Enterprise targets in our Apr 2026 tests. It was already declining in 2025 — it's not a viable production option.
For teams scraping e-commerce sites for competitor price tracking, Cloudflare is the most common protection layer on retailer and brand DTC sites. Getting this layer right has the highest ROI.
Bypassing Akamai Bot Manager v4: The TLS Problem
Akamai's detection model is architecturally different from Cloudflare's. The priority ordering is reversed: TLS fingerprinting is Akamai's primary detection signal, not a secondary one. This means curl-cffi alone (without a browser) is more effective against Akamai than against Cloudflare — and explains our 87% pass rate with curl-cffi + residential proxies.
What Akamai actually checks:
Akamai Bot Manager v4 blocks across five layers simultaneously: IP reputation, TLS fingerprinting (JA3/JA4), JavaScript telemetry, behavioral biometrics, and session continuity. The _abck cookie is generated by Akamai's sensor data script — each page load sends an encrypted payload with mouse events, keystroke timing, and device fingerprint data back to Akamai's servers.
The sensor data problem: If you're using a full browser (Camoufox, Patchright), Akamai's JS collects sensor data and validates it server-side. A browser that moves the mouse perfectly linearly or never generates scroll events will fail the behavioral check even with a clean IP and valid TLS fingerprint. We simulated human-like mouse trajectories using cubic bezier curves — this improved Akamai pass rates by ~11 percentage points over straight-line movement.
curl-cffi approach: For Akamai targets that don't require a login session, curl-cffi with impersonated TLS plus residential proxies gets 87% pass rate in our tests and is significantly cheaper to run than browser automation. At scale (10K+ requests/day), the cost difference between curl-cffi and Camoufox instances is approximately 4:1 in compute.
Where Akamai wins: Protected checkout flows and account-authenticated scraping. Akamai's session continuity tracking detects when a "new session" immediately navigates to high-value pages without natural browsing behavior. For these targets, a warm-up sequence (2–3 page loads with random dwell time before hitting the target URL) improves pass rates from 61% to 83% in our tests.
This matters particularly for product data extraction on fashion and electronics retailers — Zara, H&M, MediaMarkt, and Fnac all run Akamai, and authenticated scraping for SKU-level data requires the session continuity bypass.
PerimeterX / HUMAN: Why the 67% Ceiling Is a Hard Wall
PerimeterX — rebranded as HUMAN Security in 2023 but still widely called PerimeterX in the scraping community — is the hardest WAF to bypass reliably in 2026. Our best result, Camoufox + residential proxies, achieved 67% pass rate. That's not a tuning problem. It's architectural.
Why PerimeterX is different: Every PerimeterX deployment is trained on the specific website's historical traffic. The ML model has been fed months of real user behavior data for that specific domain — click patterns, session durations, navigation flows, device distributions. A bypass technique that works against a PerimeterX-protected fashion retailer may have a 30-point lower pass rate on a PerimeterX-protected pharmaceutical site because the behavioral baselines are completely different.
What PerimeterX checks:
- Browser fingerprint (canvas, WebGL, audio context, fonts)
- Behavioral signals (mouse trajectory, typing cadence, scroll velocity)
- Session graph (what pages were visited, in what order, with what dwell times)
- Network graph (does this IP's behavior across sessions match legitimate users?)
The Patchright advantage on HUMAN: Patchright (Playwright fork with stealth patches) outperforms Camoufox on PerimeterX by ~9 percentage points in our tests, despite Camoufox's Firefox fingerprint advantage. The reason: PerimeterX's ML was trained predominantly on Chrome traffic from real users. Camoufox's Firefox fingerprint is actually less common on many retail sites than Chromium, triggering minor statistical anomalies. Patchright's Chromium base matches the expected browser distribution better.
Honest ceiling: If you need >85% pass rates on PerimeterX-protected targets, you need a managed solution with large-scale IP rotation, continuously updated fingerprint profiles, and behavioral training data. DIY approaches hit a structural ceiling at ~70%.
We covered stealth tool specifics — including how Camoufox and Patchright compare in detail — in our Playwright stealth 2026 comparison post.
The Engineering Overhead Reality
Pass rate is only part of the cost equation. Here's what maintaining each approach at production scale (10K+ pages/day) actually costs in engineering time:
| Approach | Monthly infra cost (10K/day) | Engineering maintenance | Failure mode |
|---|---|---|---|
| curl-cffi + residential proxies | ~$120–180 | 3–5 hrs/month | TLS fingerprint updates, proxy rotation tuning |
| Patchright + residential proxies | ~$380–520 | 8–12 hrs/month | WAF model updates, fingerprint drift, Chromium updates |
| Camoufox + residential proxies | ~$440–600 | 10–15 hrs/month | Firefox binary updates, memory pressure (200MB+ per instance) |
| Managed scraping infrastructure | Custom pricing | ~1 hr/month (config) | Handled by provider SLA |
The hidden cost is WAF updates. Cloudflare ships model updates every 2–4 weeks. Akamai pushes sensor data script changes roughly monthly. Each update can drop your pass rate by 15–30 points overnight and requires debugging time to recover. Teams running competitor price monitoring at scale often find that the first six months of DIY are manageable, but month 7–12 engineering time exceeds the cost of managed infrastructure.
For teams evaluating the anti-bot landscape more broadly, this maintenance overhead is the most underestimated cost in scraping infrastructure planning.
When to Stop DIY and Use Managed Infrastructure
The break-even point we see most often: when a scraping engineer spends more than 8 hours/month on WAF maintenance, managed infrastructure is cheaper.
Stop maintaining your own bypass stack when:
- You're hitting PerimeterX at scale. The 67% ceiling means ~1 in 3 requests fails. At 10K requests/day that's 3,000 failures you're either retrying (more cost) or missing (data gaps).
- You need >90% reliability SLA. Managed providers operate large proxy pools with continuously updated fingerprint profiles that individual teams can't replicate.
- Your scraping targets are authenticated. Session management across large proxy pools is complex engineering that rarely makes sense to build in-house.
- Your team is < 5 engineers. The maintenance burden of staying ahead of WAF updates takes a meaningful percentage of a senior engineer's time.
ScrapeWise handles Cloudflare, Akamai, and PerimeterX targets as part of managed scraping infrastructure — with pass rates validated against production targets, not sandboxes. If you're spending engineer time on WAF maintenance instead of using the data, it's worth the conversation.
Paste any URL — ScrapeWise handles the anti-bot
Managed infrastructure that adapts when sites change. No proxies, no code, no per-request fees.
97% accuracy on Amazon benchmarks · no credit card · book a 15-min call →